Unlimited Possibilities of
Truth in Technicality
The Cyber Portal demonstrates how technical truth — applied with ethical precision — can drastically decrease ignorance and protect those who seek genuine understanding.
Developed by Zealous Mirror Inc. — where cybersecurity meets ethical formation.
Stop Building Happy Paths. Start Building Rollbacks.
Production-grade systems require compensating actions, not just try/except logs. The Saga Pattern is the ethical engineering standard.

When Step 3 fails, the DB is locked, GWorkspace is crashed, and there's no recovery path. A "resume-generating event."
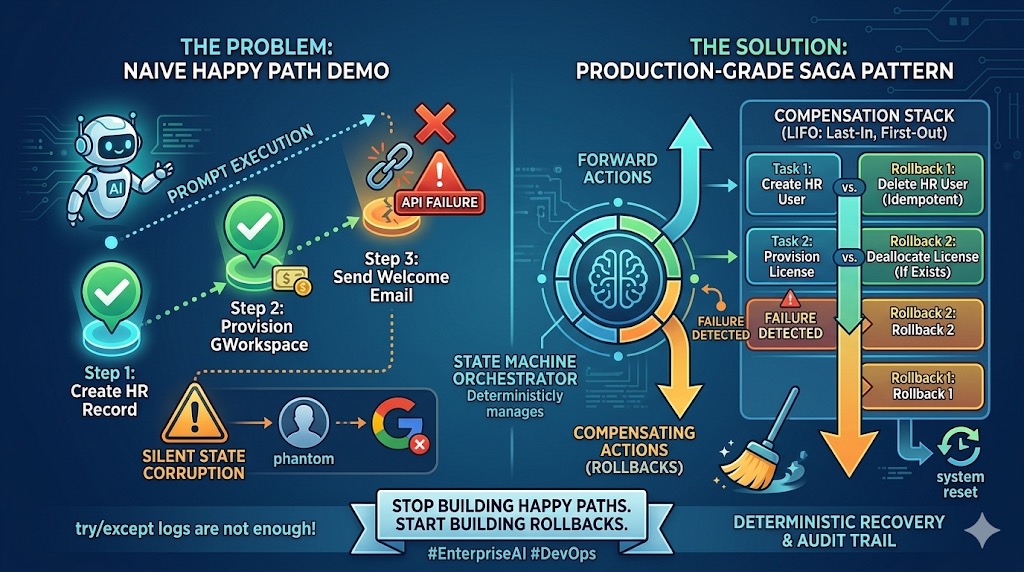
Deterministic recovery with LIFO compensation stack. Every forward action has a rollback. The State Machine Orchestrator manages it all.
DIETER in Action
Watch the DIETER Confrontation Protocol interface reveal ethical nature through data-driven analysis.
DIETER Interface — Ethical Nature Revealed
The futuristic diagnostic interface evaluates ethical thresholds across multiple dimensions. "Your ethical nature is revealed" — Zealous Mirror Inc.
Nefarious Piggyback Shield
Six layers of protection ensuring that no malicious entity can ride legitimate traffic into protected systems.
Layer 1: Perimeter Sentinel
First-contact threat detection using behavioral pattern analysis
Layer 2: Identity Verification
Multi-factor authentication with biometric integration
Layer 3: Data Encryption Matrix
End-to-end encryption with quantum-resistant algorithms
Layer 4: Behavioral Analytics
Real-time monitoring of anomalous activity patterns
Layer 5: Autonomous Response
AI-driven threat neutralization without human latency
Layer 6: Ethical Oversight
Human-in-the-loop governance ensuring proportional response
DIETER Confrontation Protocol v2
A systematic approach to confronting digital threats with ethical precision. Each phase builds on the last — no shortcuts, no collateral damage.
Detect
Identify the confrontation vector and its origin pattern
Isolate
Contain the threat without collateral system damage
Evaluate
Assess severity, intent, and ethical implications
Transform
Convert threat data into defensive intelligence
Execute
Deploy proportional countermeasures with precision
Restore
Return systems to integrity and document learnings
Autonomous Ethical Monitoring System
The system continuously monitors its own ethical boundaries. Before any action is taken, it passes through the DIETER protocol internally — ensuring that even automated responses maintain the highest ethical standards.
Minimum 80% accuracy milestone required before law enforcement applications. Phased deployment ensures no premature action.
Virtual Formation Environment
A wireframe human navigates urgent ethical notices in a neon-lit virtual environment — the future of formation technology.